DEMETER
Always Watching
Monitor Your Assets in the Data Center as well as remote users in a secure fashion
User Behavior Analytics (UBA)
Monitor User abnormal activities and respond to them immediately.
Intrusion Detection (IDS)
Detect any suspicious intrusion and generate mitigation plan.

Dark Web Monitoring (DWM)
Monitor the leaks for your organization against Deep and Dark Web Leaks.
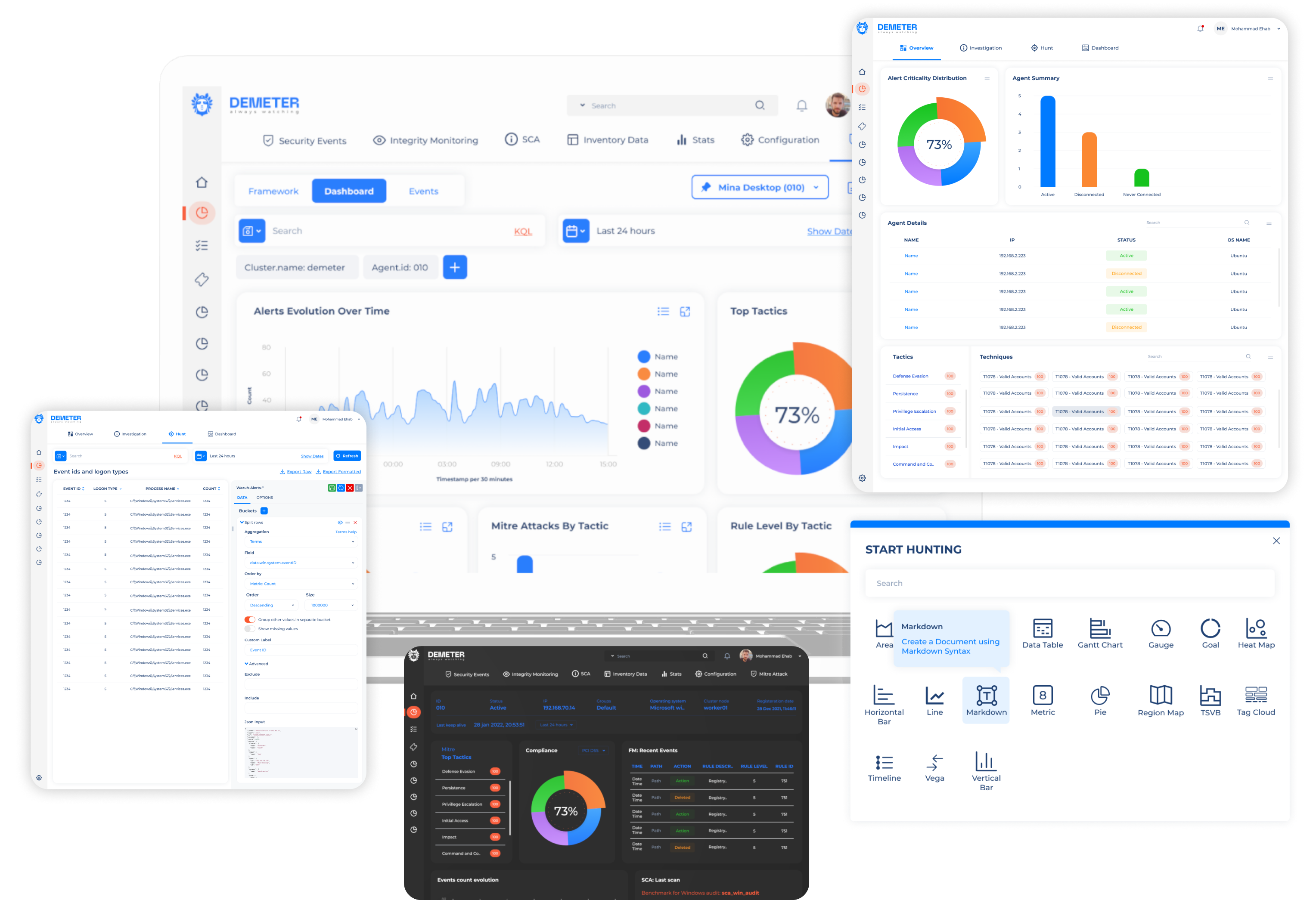
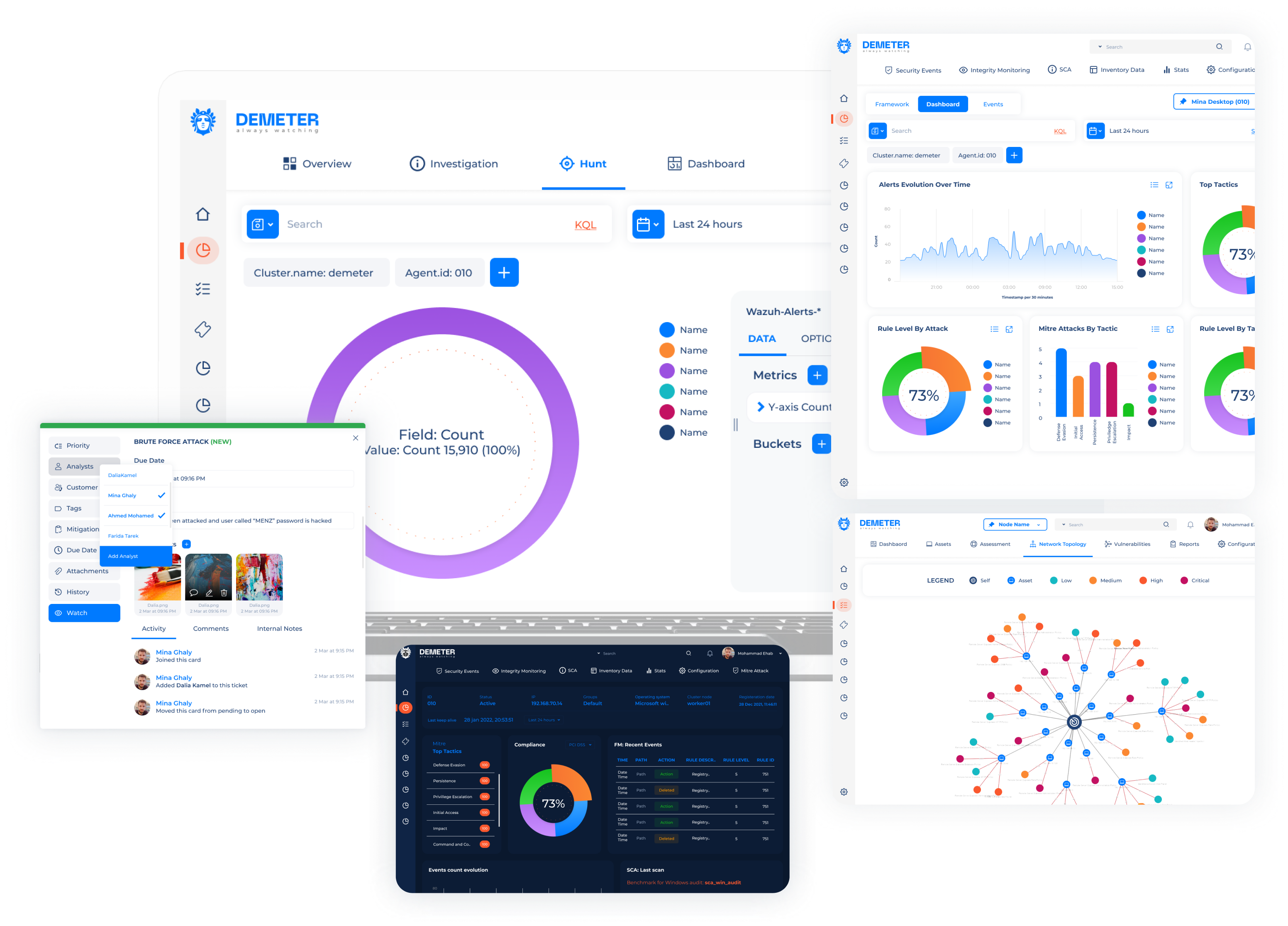
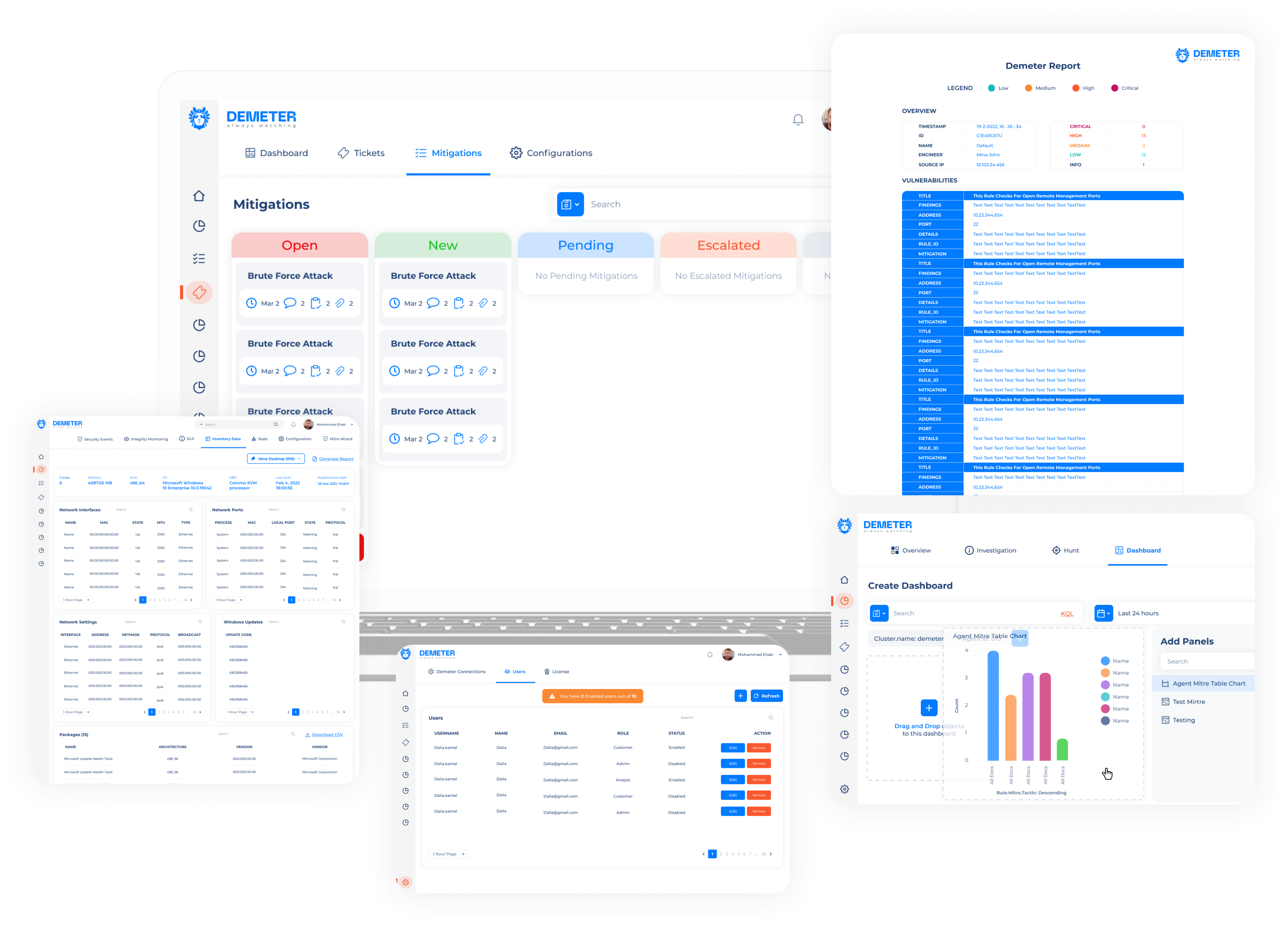
Demeter can detect Malware attacks and we can pinpoint the beginning of the infection.
Demeter can manage Windows Mac OSX and Linux from a Single Interface.
Demeter can capture and analyse suspicious traffic and capture files for further analysis.